Introduction
This chapter provides an overview of purple teaming and how it compares to other forms of technical testing. It also explores considerations on whether to establish an internal purple team or procure services from an external vendor. The chapter concludes with technical considerations, including offensive tooling, test environments and progress tracking options.
Chapter Content
This section provides reproductions of the key figures and code snippets seen in this chapter.
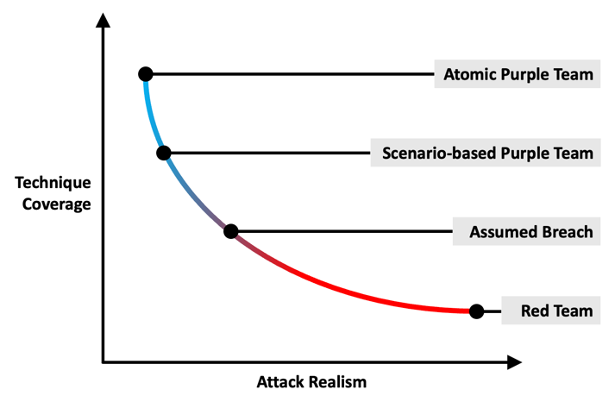
Methodology Selection
Resources
The following resources expand on topics covered in this chapter.
Assumed Breach Testing
A report on the compromise of SolarWinds and subsequent large scale supply chain attack by the Russian SVR
Kim Zetter, "The Untold Story of the Boldest Supply-Chain Hack Ever" Wired, May, 2023
Read MoreA report from Lily Haw Newman in the early days of the Log4j vulnerability disclosure, highlighting the scale and impact of the security flaw
Lily Hay Newman, "'The Internet Is on Fire'" Wired, December, 2021
Read MoreOffensive Tooling
Highlights of Cobalt Strike's featureset, including its customizability and post-exploitation capabilities
"Features", Fortra, accessed January, 2025
Read MoreFeatures of Bishop Fox's Sliver C2 framework, including mTLS communications and compile-time obfuscation
"Sliver", Bishop Fox, accessed January, 2025
Read MoreCody Thomas's Mythic C2 framework, including cross-platform agent support and remarkable extensibility
"Mythic", Cody Thomas, accessed January, 2025
Read MoreThe Havoc C2 framework, developed by Paul Ungur, with its flagship Demon agent, that includes features like patching of ETW and AMSI via hardware breakpoints and sleep obfuscation
"6. Agent.md", Paul Ungur, accessed January, 2025
Read More